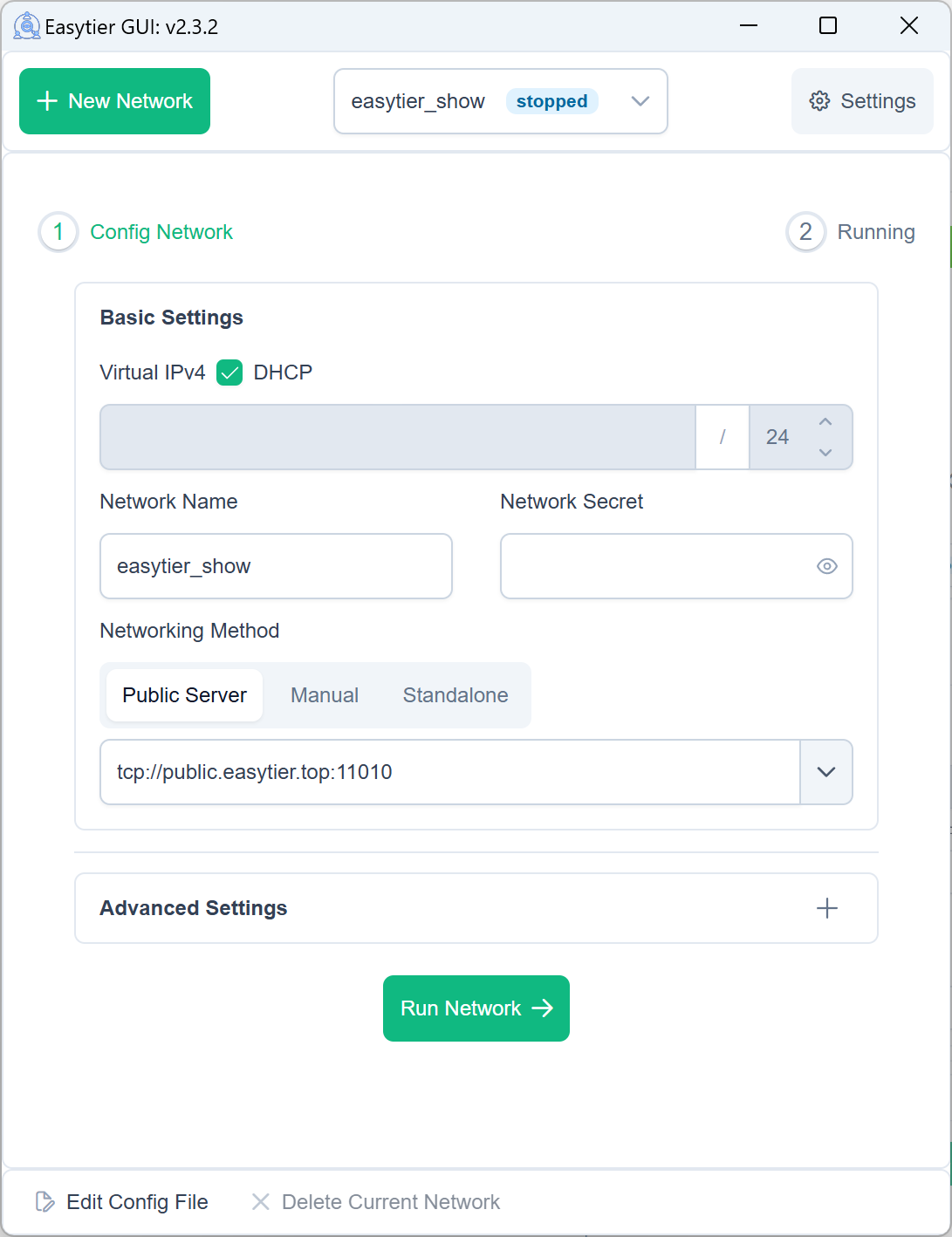
The GUI exposed three networking modes: public server, manual, and standalone. In practice EasyTier does not have a server/client role distinction here. Those options only mapped to different peer bootstrap shapes, which made the product model misleading and pushed users toward a non-existent "public server" concept. This change rewrites the shared configuration UX around initial nodes. Users now add or remove one or more initial node URLs directly, and the UI explains that EasyTier networking works like plugging in a cable: once a node connects to one or more existing nodes, it can join the mesh. Initial nodes may be self-hosted or shared by others. To preserve compatibility, the frontend keeps the legacy fields and adds normalization helpers in the shared NetworkConfig layer. Old configs are read as initial_node_urls, while saves, runs, validation, config generation, and persisted GUI config sync still denormalize back into the current backend shape: zero initial nodes -> Standalone, one -> PublicServer, many -> Manual. This avoids any proto or backend API change while making old saved configs and imported TOML files load cleanly in the new UI. Code changes: - add initial_node_urls plus normalize/denormalize helpers in the shared frontend NetworkConfig model - remove the mode switch and public-server/manual specific inputs from the shared Config component and replace them with a single initial-node list plus explanatory copy - update Chinese and English locale strings for the new terminology - normalize configs received from GUI/web backends and denormalize them before outbound API calls - normalize GUI save-config events before storing them in localStorage so legacy payloads remain editable under the new model
EasyTier
✨ A simple, secure, decentralized virtual private network solution powered by Rust and Tokio
📚 Full Documentation | 🖥️ Web Console | 📝 Download Releases | 🧩 Third Party Tools | ❤️ Sponsor
Features
Core Features
- 🔒 Decentralized: Nodes are equal and independent, no centralized services required
- 🚀 Easy to Use: Multiple operation methods via web, client, and command line
- 🌍 Cross-Platform: Supports Win/MacOS/Linux/FreeBSD/Android and X86/ARM/MIPS architectures
- 🔐 Secure: AES-GCM or WireGuard encryption, prevents man-in-the-middle attacks
Advanced Capabilities
- 🔌 Efficient NAT Traversal: Supports UDP and IPv6 traversal, works with NAT4-NAT4 networks
- 🌐 Subnet Proxy: Nodes can share subnets for other nodes to access
- 🔄 Intelligent Routing: Latency priority and automatic route selection for best network experience
- ⚡ High Performance: Zero-copy throughout the entire link, supports TCP/UDP/WSS/WG protocols
Network Optimization
- 📊 UDP Loss Resistance: KCP/QUIC proxy optimizes latency and bandwidth in high packet loss environments
- 🔧 Web Management: Easy configuration and monitoring through web interface
- 🛠️ Zero Config: Simple deployment with statically linked executables
Quick Start
📥 Installation
Choose the installation method that best suits your needs:
Linux (Recommended):
curl -fsSL "https://github.com/EasyTier/EasyTier/blob/main/script/install.sh?raw=true" | sudo bash -s install
Homebrew (MacOS/Linux):
brew tap brewforge/chinese
brew install --cask easytier-gui
Windows (Recommended, run with administrator privileges):
irm "https://github.com/EasyTier/EasyTier/blob/main/script/install.ps1?raw=true" | iex
Install via cargo (Latest development version):
cargo install --git https://github.com/EasyTier/EasyTier.git easytier
Install pre-built binary (Recommended, All platforms supported)
Additional steps:
One-Click Register Service (Automatically start when the system boots and run in the background)
🚀 Basic Usage
Quick Networking with Shared Nodes
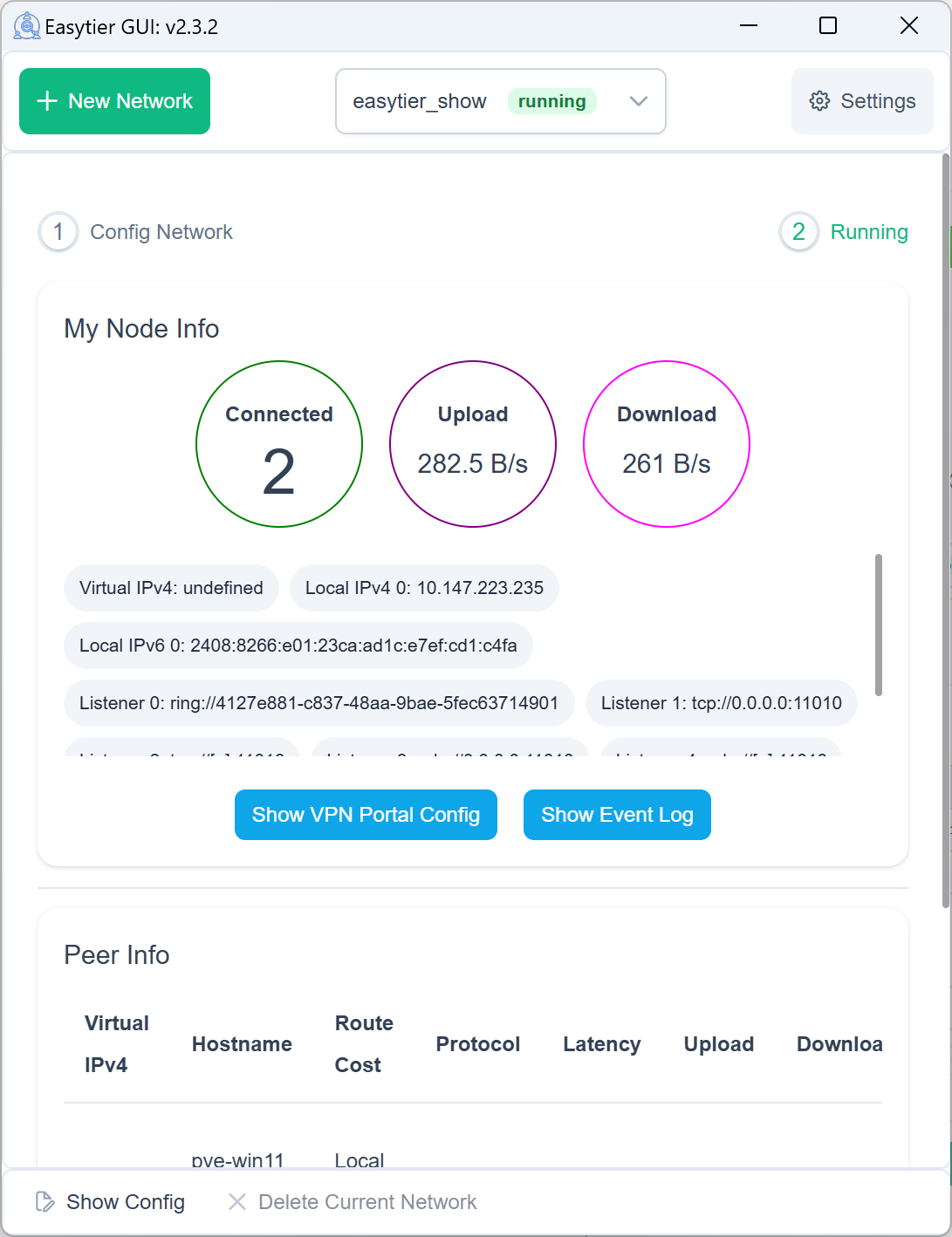
EasyTier supports quick networking using shared public nodes. When you don't have a public IP, you can use the free shared nodes provided by the EasyTier community. Nodes will automatically attempt NAT traversal and establish P2P connections. When P2P fails, data will be relayed through shared nodes.
When using shared nodes, each node entering the network needs to provide the same --network-name and --network-secret parameters as the unique identifier of the network.
Taking two nodes as an example (Please use more complex network name to avoid conflicts):
- Run on Node A:
# Run with administrator privileges
sudo easytier-core -d --network-name abc --network-secret abc -p tcp://<SharedNodeIP>:11010
- Run on Node B:
# Run with administrator privileges
sudo easytier-core -d --network-name abc --network-secret abc -p tcp://<SharedNodeIP>:11010
After successful execution, you can check the network status using easytier-cli:
| ipv4 | hostname | cost | lat_ms | loss_rate | rx_bytes | tx_bytes | tunnel_proto | nat_type | id | version |
| ------------ | -------------- | ----- | ------ | --------- | -------- | -------- | ------------ | -------- | ---------- | --------------- |
| 10.126.126.1 | abc-1 | Local | * | * | * | * | udp | FullCone | 439804259 | 2.5.0-70e69a38~ |
| 10.126.126.2 | abc-2 | p2p | 3.452 | 0 | 17.33 kB | 20.42 kB | udp | FullCone | 390879727 | 2.5.0-70e69a38~ |
| | PublicServer_a | p2p | 27.796 | 0.000 | 50.01 kB | 67.46 kB | tcp | Unknown | 3771642457 | 2.5.0-70e69a38~ |
You can test connectivity between nodes:
# Test connectivity
ping 10.126.126.1
ping 10.126.126.2
Note: If you cannot ping through, it may be that the firewall is blocking incoming traffic. Please turn off the firewall or add allow rules.
To improve availability, you can connect to multiple shared nodes simultaneously:
# Connect to multiple shared nodes
sudo easytier-core -d --network-name abc --network-secret abc -p tcp://<SharedNodeIP1>:11010 -p udp://<SharedNodeIP2>:11010
Once your network is set up successfully, you can easily configure it to start automatically on system boot. Refer to the One-Click Register Service guide for step-by-step instructions on registering EasyTier as a system service.
Decentralized Networking
EasyTier is fundamentally decentralized, with no distinction between server and client. As long as one device can communicate with any node in the virtual network, it can join the virtual network. Here's how to set up a decentralized network:
- Start First Node (Node A):
# Start the first node
sudo easytier-core -i 10.144.144.1
After startup, this node will listen on the following ports by default:
- TCP: 11010
- UDP: 11010
- WebSocket: 11011
- WebSocket SSL: 11012
- WireGuard: 11013
- Connect Second Node (Node B):
# Connect to the first node using its public IP
sudo easytier-core -i 10.144.144.2 -p udp://FIRST_NODE_PUBLIC_IP:11010
- Verify Connection:
# Test connectivity
ping 10.144.144.2
# View connected peers
easytier-cli peer
# View routing information
easytier-cli route
# View local node information
easytier-cli node
For more nodes to join the network, they can connect to any existing node in the network using the -p parameter:
# Connect to any existing node using its public IP
sudo easytier-core -i 10.144.144.3 -p udp://ANY_EXISTING_NODE_PUBLIC_IP:11010
🔍 Advanced Features
Subnet Proxy
Assuming the network topology is as follows, Node B wants to share its accessible subnet 10.1.1.0/24 with other nodes:
flowchart LR
subgraph Node A Public IP 22.1.1.1
nodea[EasyTier<br/>10.144.144.1]
end
subgraph Node B
nodeb[EasyTier<br/>10.144.144.2]
end
id1[[10.1.1.0/24]]
nodea <--> nodeb <-.-> id1
To share a subnet, add the -n parameter when starting EasyTier:
# Share subnet 10.1.1.0/24 with other nodes
sudo easytier-core -i 10.144.144.2 -n 10.1.1.0/24
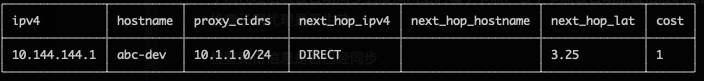
Subnet proxy information will automatically sync to each node in the virtual network, and each node will automatically configure the corresponding route. You can verify the subnet proxy setup:
- Check if the routing information has been synchronized (the proxy_cidrs column shows the proxied subnets):
# View routing information
easytier-cli route
- Test if you can access nodes in the proxied subnet:
# Test connectivity to proxied subnet
ping 10.1.1.2
WireGuard Integration
EasyTier can act as a WireGuard server, allowing any device with a WireGuard client (including iOS and Android) to access the EasyTier network. Here's an example setup:
flowchart LR
ios[[iPhone<br/>WireGuard Installed]]
subgraph Node A Public IP 22.1.1.1
nodea[EasyTier<br/>10.144.144.1]
end
subgraph Node B
nodeb[EasyTier<br/>10.144.144.2]
end
id1[[10.1.1.0/24]]
ios <-.-> nodea <--> nodeb <-.-> id1
- Start EasyTier with WireGuard portal enabled:
# Listen on 0.0.0.0:11013 and use 10.14.14.0/24 subnet for WireGuard clients
sudo easytier-core -i 10.144.144.1 --vpn-portal wg://0.0.0.0:11013/10.14.14.0/24
- Get WireGuard client configuration:
# Get WireGuard client configuration
easytier-cli vpn-portal
- In the output configuration:
- Set
Interface.Addressto an available IP from the WireGuard subnet - Set
Peer.Endpointto the public IP/domain of your EasyTier node - Import the modified configuration into your WireGuard client
- Set
Self-Hosted Public Shared Node
You can run your own public shared node to help other nodes discover each other. A public shared node is just a regular EasyTier network (with same network name and secret) that other networks can connect to.
To run a public shared node:
# No need to specify IPv4 address for public shared nodes
sudo easytier-core --network-name mysharednode --network-secret mysharednode
Related Projects
- ZeroTier: A global virtual network for connecting devices.
- TailScale: A VPN solution aimed at simplifying network configuration.
Contact Us
- 💬 Telegram Group
- 👥 [QQ Group]
License
EasyTier is released under the LGPL-3.0.
Sponsor
CDN acceleration and security protection for this project are sponsored by Tencent EdgeOne.
Special thanks to Langlang Cloud and RainCloud for sponsoring our public servers.
If you find EasyTier helpful, please consider sponsoring us. Software development and maintenance require a lot of time and effort, and your sponsorship will help us better maintain and improve EasyTier.